BitTorrent and uTorrent are the two major platforms for downloading large files.
You can download almost any type of file.
You can download videos, images, infographics, and even download games as well.
To use one of these software, you need to open your web browser and need to search for uTorrent or BitTorrent.
When you search for that, you’ll find several results.
Make sure to click on the first result and land on the official website.
Once you reach the official website, now, you need to download the application or software program.
Once the application or software is downloaded to your laptop or PC, now, you need to install it.
Once the application or software is installed, now, you’re ready to use it. To use one of these platforms, you need to open it and need to download the torrent file first.
Suppose, you need to download a game file GTA5.
To download GTA5, you first need to download its torrent file.
Once you download the torrent file, now, you need to open the application or software and upload the file.
Once the file is uploaded, now, you need to click on the DOWNLOAD button to download the GTA5.
When you click on the download button, your download will start.
Once the download starts, now, you can see all the stats and everything you need to know about the file.
It’s all about the download process of the uTorrent or BitTorrent.
Sometimes, you may come across the question of how the uTorrent or BitTorrent algorithm works.
How the things download using uTorrent or BitTorrent?
Well, if this is the case then make sure to stay with me and read the article to understand the working principle of the uTorrent or BitTorrent.
uTorrent and BitTorrent both work on the principle of the BitTorrent protocol. It’s a peer-to-peer file-sharing system.
To download a file using any of these software programs, you need to first download the torrent file.
A torrent file contains the information of the main file.
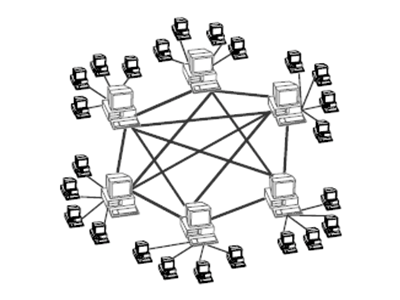
A peer-to-peer file-sharing system is a communication medium for sharing files and folders.
In this system, a group of systems communicate with each other and share files and folders.
There are two types of PEER-TO-PEER networks.
Make sure to stay with me and read the article to understand the functionality and working principle of the P2P system.
1. Pure P2P network
2. Hybrid P2P network
Let’s discuss both of these in detail to understand the workings of both of these systems.
Read more:-
1. Pure P2P network:
In this system, there is not any server for the communication of the peers or systems.

These systems communicate directly with each other and there is not any medium like servers or a lead peer.
2. Hybrid P2P network:
In this network, there is a middle entity for the communication.
If there is a need to share files or folders then there is a middle server to communicate with each other.
In this protocol, you’ll find certain entities.
Make sure to read this article further to understand everything you need to know about the parts of the protocols.
- Tracker
- Static meta info file
- Original downloader
- End-user/downloader
Let’s move further and discuss all of these in detail. Make sure to stay with me and read the article further.
- Tracker:
A tracker is a central server that keeps on tracking the peers or systems.
It’s placed to track the service providers.
- Static meta info file:
As the name suggests, STATIC META INFO FILE is a torrent file that contains all the information of the tracker server.
It contains the IP addresses of the files and folders that you want to download to your system.
- Original downloader:
As the name suggests, it’s a full file system that has the file you want to download.
Suppose, you want to download a file then you’ll download its torrent file upload the file on the software, and start downloading the file.
Once the file will downloaded, now, the parts of the files are downloaded from different systems or peers.
Now, if you downloaded the full file then you’ll behave like a FEEDER or original downloader because you have the complete file.
- End-user/downloader:
Last but not least, it’s a peer or system that has a partial file or incomplete file.
Suppose, you started downloading the file, now, if you don’t have the complete file then you’ll behave like an END-USER.
So, it’s all about the architecture of the BitTorrent protocol.
If you want to download a file then you may need to know about the protocol and everything related to it.
If you have any questions about any of these terms then make sure to mention them in the comments down below.
BitTorrent allows the downloading of the files into pieces.
It’s a decentralized system and requires several PCs to download the files and folders.
Now we understand the functionality and working principles and also the parts of the architecture of the BitTorrent protocol.
Now, let’s move further and discuss the distribution of the content files and folders in the BitTorrent protocol. Let’s move further and deep dive into the details of the BitTorrent protocol functioning.
Read more:-
Download Torrent Using UC Browser – Explain
Downgrade uTorrent Software And Application
Piece selection algorithm:
If you want to download something then in BitTorrent as we know there should be a piece selection algorithm to avoid the download failing.
In a swarm network of peers if there is a file that needs to be downloaded and a piece of that file is missing then the process of the download will fail and the whole swarm will break.
Which is not desirable and shouldn’t happen with the peers.
To prevent it, the BitTorrent protocol needs to make sure about the PIECE selection algorithm.
There are four parts that you may need to understand.
Make sure to read the article in deep to understand this.
1. Random first piece:
In this selection, a peer quickly selects any piece of the file and starts downloading and uploading the same.
In this, there is no required selection and the process of uploading and downloading will start quickly.
2. Rarest first:
As the name suggests, in this the swarm selects the rarest piece of the file starts downloading first, and replicates it to avoid the interruption of the slow downloading speed and also the loss of the file.
3. Strict Policy:
As I told you earlier, if you want to download a file then before downloading a file, there has to be divided the file into pieces and then sub-pieces.
If a piece of the file is requested then all the sub-pieces of a piece of the file need to download first and then the remaining files will download.
4. Endgame mode:
When a piece of the file is requested for downloading then there is slow uploading of the file to ensure that the file needs to download first.
Once the download is finished the uploading speed boosts itself to provide the availability of the file for the swarm.
These are the policies for downloading a file from a swarm of a network.
These policies have to be implemented to avoid network failure or breaking of the swarm.
CHOCKING:
Now, there is a term called Choacking. It’s a tit-for-tat mechanism to get consistent download speed.
It’s a process of refusing the upload when the file is downloading.
It helps boost the speed to download the files faster rate.
At a given point in time, there have to be 4 peers who can be unchecked.
To prevent the slow upload speed, 4 peers can be unchecked.
Optimistic Unchoking:
Apart from 4 unchoking, there is an additional unchoking. It’s not related to boosting the download speed, it’s related to identifying the unused connection.
The unused connection has to be eliminated or needs to be removed from the swarm so that, other peers will be available for the connection.
Anti-snubbing:
It’s again a good term to avoid the interruption of the network break.
If a peer didn’t receive anything from the last 60 seconds then it has to be considered as the snubbed peer.
Upload only:
As the name suggests, if a peer completes the file download and there is nothing to download from the network then there is only one thing that happens called the upload.
If a swarm has only uploaded then it is called UPLOAD only.
Advantages and uses:
- Distributing large files like Linux ISO images.
- Distributing Software patches and updates.
- Is being done by Blizzard Entertainment Inc., to distribute updates for the World of Warcraft
- Distributing popular files that have high traffic for relatively short periods
- Unlike traditional server/client downloads, high traffic leads to more efficient file sharing via BitTorrent.
Disadvantages and Security issues:
- An easy distribution method for pirated/illegal content
- Cannot modify/update the file to newer versions once the torrent has been distributed
- The IP of all peers and info of files they are downloading are publicly available on trackers
- The tracker is a critical component and if it fails it can disrupt the distribution of all the files it has tracking.
It’s all about the BitTorrent protocol. I hope you understand everything in a BitTorrent protocol.
If you have anything remaining then make sure to mention it in the comments down below.
Read more:-
Can I Get Caught If I Use uTorrent – Explain
Should I Stop The Seeding In uTorrent – Explain
Bottom lines:
I hope you guys understand the working mechanism of the BitTorrent protocol.
Well, it can be a great way of distributing the files and folders but it still has a few limitations.
As I explained above all the disadvantages.
If you still have remaining questions in your brain then you can mention them in the comments down below.
Make sure to carefully read the article and don’t forget to share it on your social media handles.